Endor Labs detects malware in dependencies by scanning the packages used in the project and recognizing known malicious patterns. Monitoring for known malicious packages: Endor Labs scans dependencies to identify malware by cross-referencing findings with the Open Source Vulnerability (OSV) database and data from the proprietary malware feed. Suspicious code behavior: Endor Labs uses malware detection rules and SAST rules to scan open source package dependencies for suspicious code patterns and behaviors. These rules analyze code structures, detect anomalies, and identify potential threats.Documentation Index
Fetch the complete documentation index at: https://docs.endorlabs.com/llms.txt
Use this file to discover all available pages before exploring further.
Detect malware findings
Endor Labs provides a set of malware policies designed to identify and manage malicious or suspicious code in your project, ensuring that Endor Labs detects potential security risks early.- The OSS finding policy detects malicious code and findings in your project. You can edit the policy to change the severity and template parameters.
- Configure malware action policy to specify how detected malware findings should be handled automatically, including notifications, blocking actions, and workflow triggers.
- Configure malware exception policy to exclude malware findings under defined conditions. This filters out false positives and keeps the focus on critical risks.
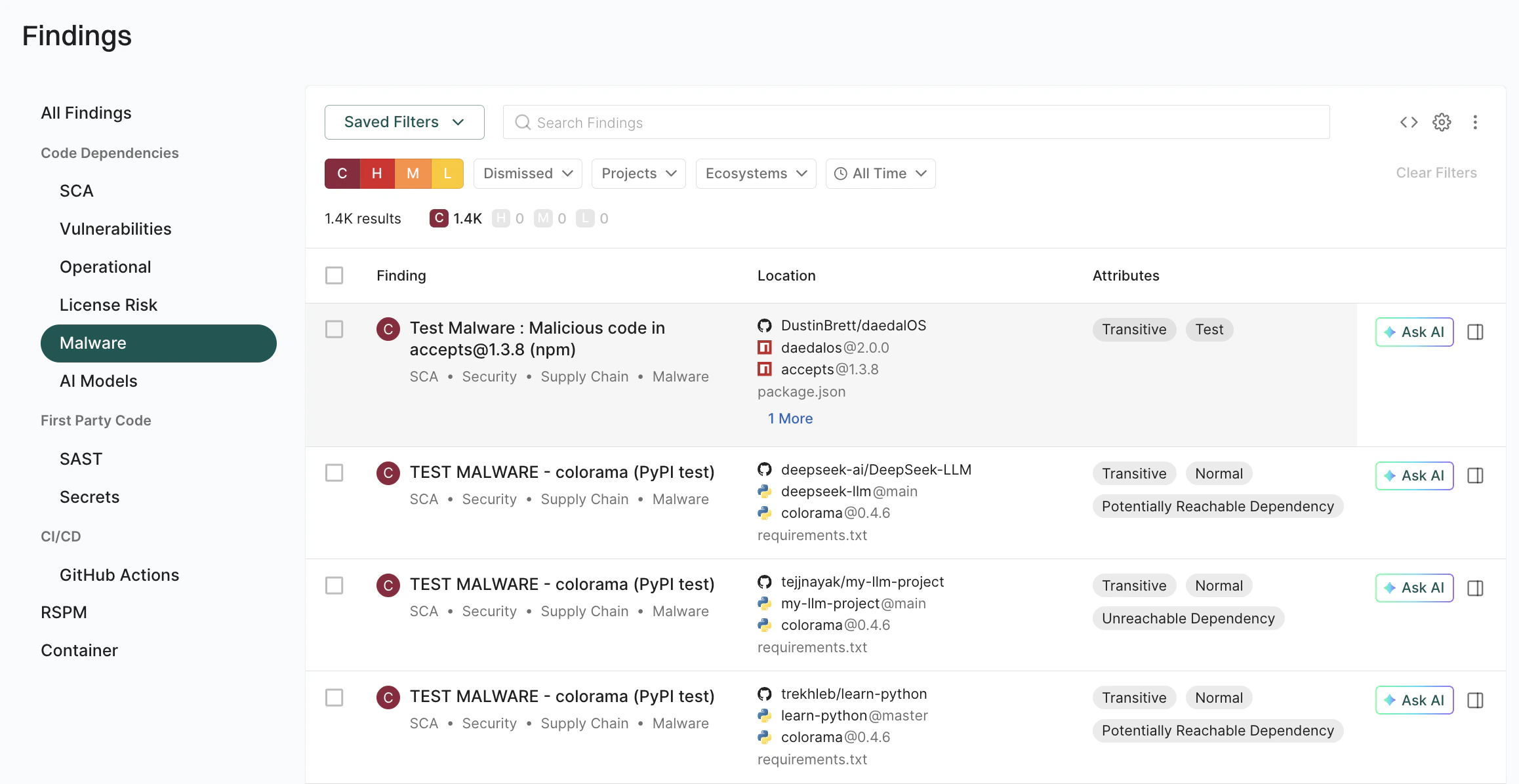
View malware findings
You can view the malware findings, prioritize them, and take corrective action.- Sign in to Endor Labs and select Projects from the left sidebar.
- Select the project for which you want to view the malware.
-
Select Malware under Code Dependencies to view malware findings.
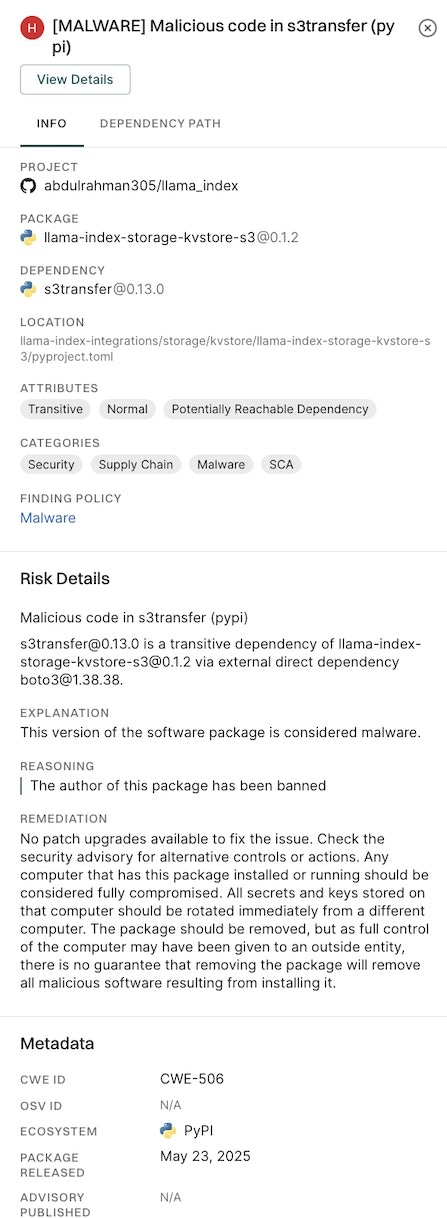
- Select a finding to view detailed information of the malware in the right sidebar. The right sidebar contains the following information:
- Project: The name of the project where Endor Labs finds the malware, finding policy, categories, and attributes of the project.
-
Risk Details:
- Explanation of the finding.
- Reasoning explains why Endor Labs classifies the package as malware.
- Recommended remediation.
-
Metadata: Contains details such as the vulnerability IDs, ecosystem, package release date, and advisory publication date.
-
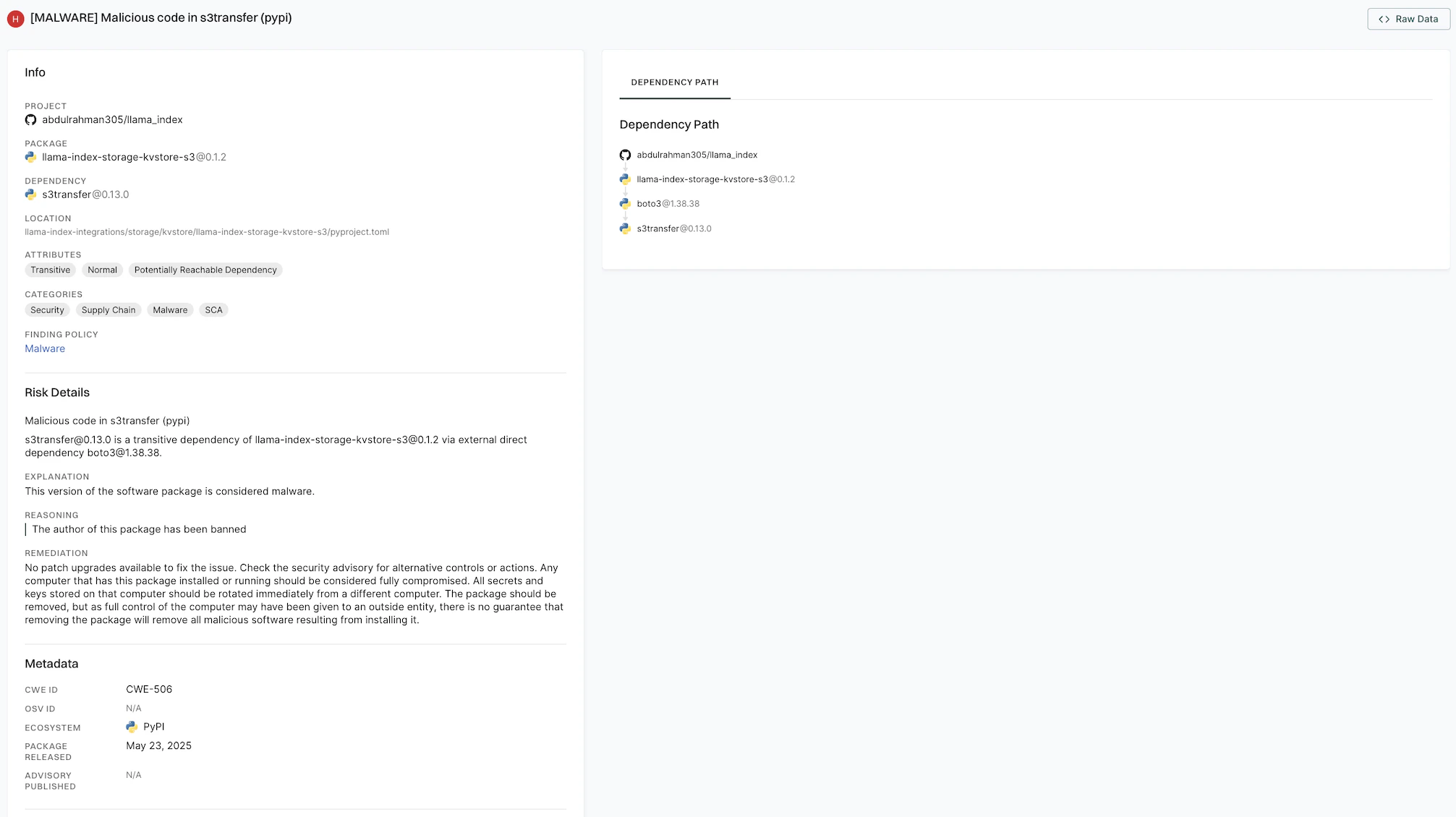
Click View Details, then select Dependency Path to view the dependency path.
Check for malicious package versions
You can check whether specific package versions are flagged as malicious by querying the Endor Labs malware database. Run the following command to make an API query. The namespace must beoss, and you can pass one or more package versions in the names list.
MailBee@12.3.3 package version is malicious.

