All findings are enabled, disabled and/or customized via policies. There are three types of Finding Policies:Documentation Index
Fetch the complete documentation index at: https://docs.endorlabs.com/llms.txt
Use this file to discover all available pages before exploring further.
- Open-source software management - Enable or disable findings for Vulnerabilities and Malicious Packages, Outdated Dependencies, Recently Released Dependencies, Unmaintained Dependencies, Unpinned Direct Dependencies, Unused Direct Dependencies, License Risks
- Repository security posture management configuration - Enable, disable, or customize out-of-the-box policies repository security posture management (RSPM)
- Custom - Create custom policies from scratch or from pre-defined policy templates
Manage finding policies
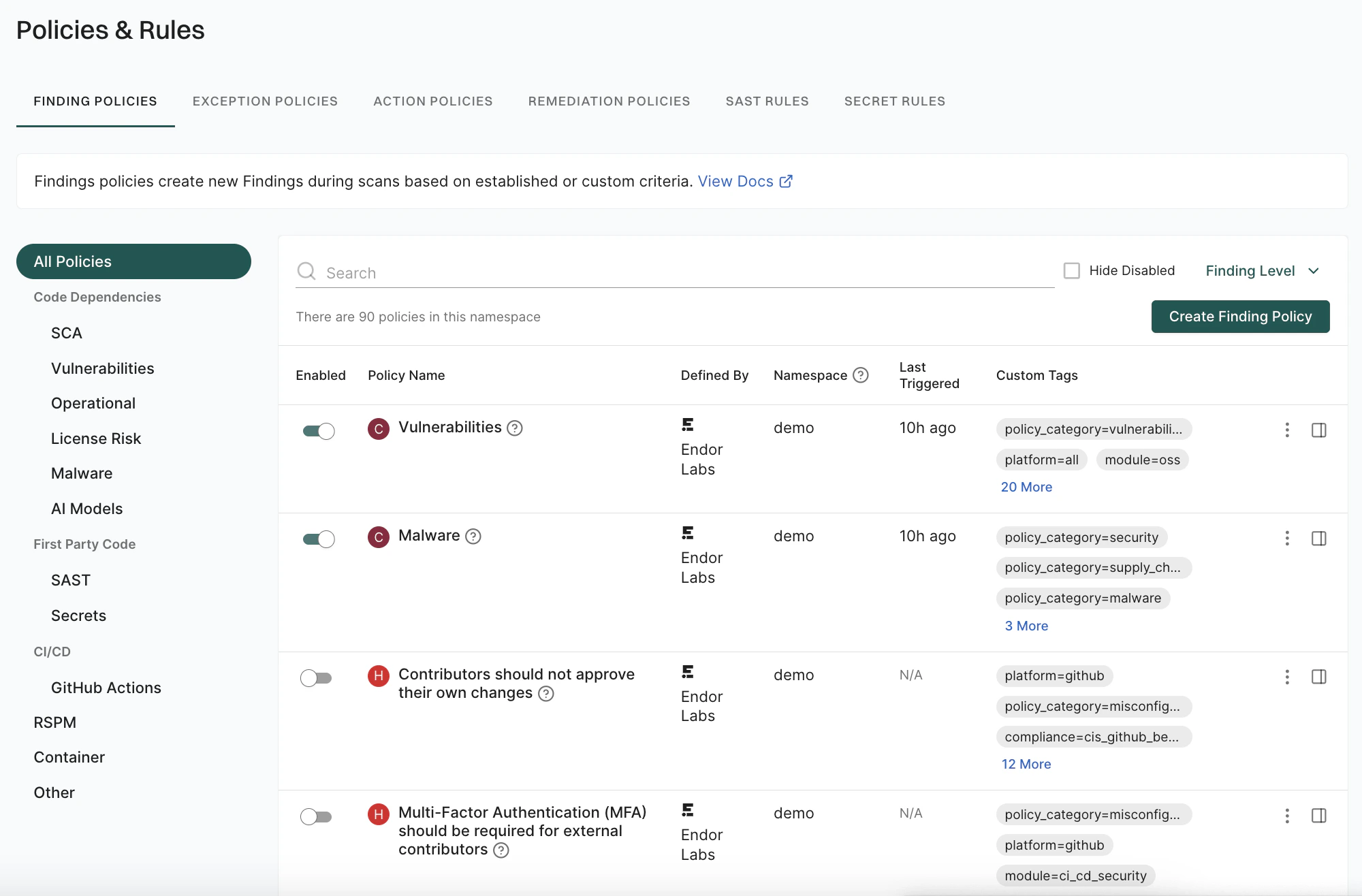
You can view, enable, disable, edit, upgrade, or delete your Endor Labs finding policies.- Sign in to Endor Labs and select Policies & Rules from the left sidebar.
- Select Finding Policies to view the list of finding policies.
- The preset filters help you locate the finding policies that matter most to you. Select a category to narrow down and focus on the relevant policies.
- Enter text in the search bar to find a policy by name or keyword.
- Use the toggle next to a finding policy to enable or disable the finding policy.
- Select Hide Disabled to hide policies that are not enabled.
- Use Finding Level to filter policies by Critical, High, Medium, or Low.
- To edit a policy, click on the vertical three dots and select Edit.
- To delete a policy, click on the vertical three dots and select Delete. The findings associated with the policy are not deleted.
Upgrade a finding policy
Upgrades are available when there are changes to a policy, such as new fields, parameters, tags, or updates to the Rego code. After upgrading a policy, you can’t revert it to its previous version. You can upgrade a policy to the latest template version in any of the following two ways:- Click on the vertical three dots and select Upgrade and click Upgrade Policy.
- Click on Upgrade Available, review the release notes and click Upgrade Policy.
You can upgrade finding policies if you have admin permissions.
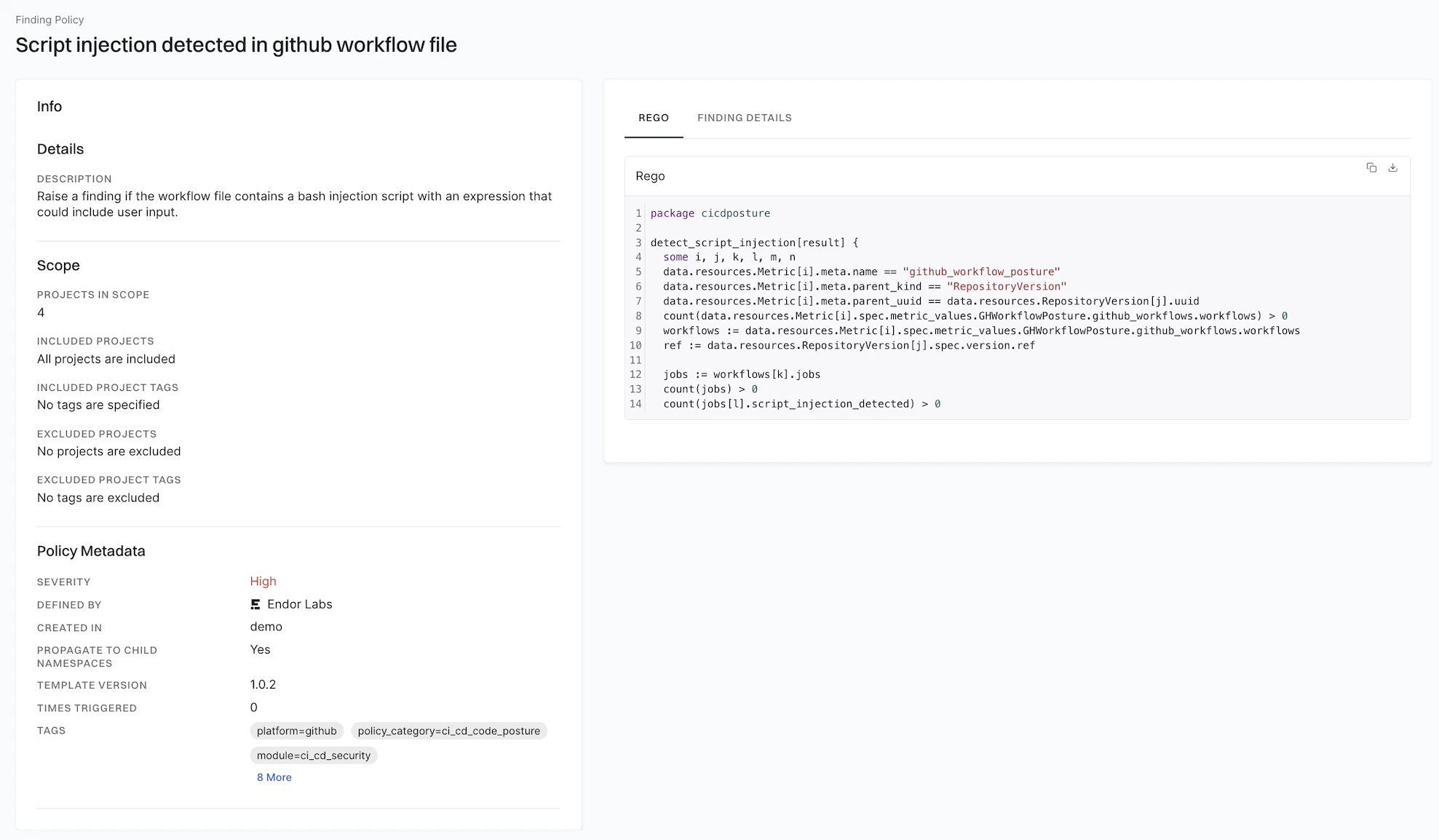
View policy details
- Sign in to Endor Labs and select Policies & Rules from the left sidebar.
- Select Finding Policies to view the list of finding policies.
-
Select a policy you want to review and click View Details.
You can see the policy’s description, scope, and metadata. You can review the severity, finding categories, explanatory details, remediation steps and the Rego rules that implement the policy logic.
Custom finding policies
Create custom finding policies to identify additional issues based on the needs of your organization. For example, you can create license violation policies to define the behavior for missing, unknown, problematic, or incompatible licenses. You can permit or restrict packages with certain license types. Endor Labs provides finding policy templates for multiple use cases:Create a finding policy from template
Create a finding policy from a pre-defined Endor Labs template.- Sign in to Endor Labs, and select Policies & Rules from the left sidebar.
- Click Create Finding Policy.
- Choose From Template to create a finding policy from template.
- Choose a Template Category from the list.
- Choose a Policy Template from the list. The template details are pre-filled with recommended values on the form.
- Endor Labs pre-populates Severity, Summary, Explanation, Remediation, Finding Name, and Finding Categories with recommended values. You can modify these fields except Finding Categories.
- In Finding Custom Tags, enter custom tags that you want to associate with the findings of this policy. Custom tags can have a maximum of 255 characters and can contain letters, numbers, and characters = @ _ -. These are different and separate from the system defined finding tags.
- You can Assign Scope to the finding policy by specifying what projects the policy has to scan.
- In Inclusions, enter the projects and the tags of the projects that you want to scan.
- In Exclusions, enter the projects and the tags of the projects that you do not want to scan. Exclusions take precedence over the inclusions, in case of a conflict.
- Click the link to view the projects included in the finding policy scan.
- Click Add project tag to these projects and enter a tag for the selected projects. Click Save Tags to apply it or Reset Tags to discard changes.
- You can set custom tags for your projects from Projects > Settings > Custom Tags. See Tagging projects for more information about creating project tags.
- Name Your Finding Policy.
- Enter a human readable Name for your finding policy.
- Enter a Description for your finding policy that describes what it does.
- Enter any Policy Tags that you want to associate with your policy. Tags can have a maximum of 255 characters and can contain letters, numbers, and characters = @ _ -.
- Advanced: When you define a policy you do so for the current namespace and all child namespaces. If you do not want the policy to be applied to any child namespaces, click Advanced and deselect Propagate this policy to all child namespaces.
- Click Create Finding Policy. The policy will be enabled by default.
Rescan the project to apply the newly created finding policy and update the findings.
Create a finding policy from scratch
Write a finding policy from scratch using the OPA Rego policy language.- Sign in to Endor Labs, and select Policies & Rules from the left sidebar.
- Click Create Finding Policy.
- Choose From Scratch to author a finding policy from scratch.
-
Enter the Rego rule for the policy in Rego Definition. For instance, the following Rego rule identifies dependencies with an Endor Labs overall score lower than 7.
-
Enter the OPA Query Statement for the rule in the following format:
data.<package-name>.<function-name>. For the example, the query statement isdata.examples.match_package_version_scorein the above Rego rule. -
Select the Resource Kinds required to evaluate the policy. For the example above the required resource kinds are
PackageVersionandMetric. - In Group by Fields, if applicable, list which custom output fields to group the findings by in addition to the resource UUID. Use this optional field if you want to be able to raise multiple findings against the same finding target. For example, a repository version may have multiple exposed secrets and thus there are multiple findings of the same type for the same repository version. You do not need to add all (or any) custom fields here, just the ones you want to be used to group the matches by.
- Choose a Severity for the generated finding.
- Enter a short Summary of the finding.
- Enter an Explanation for the finding. You can include additional information or explain why this finding is important.
- Describe how to mitigate the finding in Remediation.
- Enter the Finding Name.
- Select one or more categories for the finding in Finding Categories.
- See steps 6-10 above under Create a finding policy from template
The application verifies the Rego syntax and query statement before creating the policy. However, the logic cannot be fully validated without input data. See also validate policy.
Available resource kinds
Every policy must specify the resource kinds it needs to execute the Rego logic. Requested resource kind objects for the current scan are made available to the Rego code underdata.resources.<ResourceKind>. The following resource kinds are available:
Finding targets
Findings are raised against finding targets. Findings targets have one of three resource kinds:- Repository (for example, default branch protections)
- RepositoryVersion (for example, CI/CD coverage, secrets)
- PackageVersion (for example, vulnerabilities, scores, licenses)
The finding target resource kind is PackageVersion for findings in the root package as well as for findings in its dependencies. A dependency PackageVersion record may or not be in the same namespace as the root package. The relationships between the root package and its dependencies is captured by the corresponding DependencyMetadata records. All DependencyMetadata records are children of the root PackageVersion record in the same namespace as the root PackageVersion.
Expected output format
All finding policies must generate the finding payload as json data, listing the finding target resource kind and UUID under “Endor” in the following format.Custom output fields
Custom key-value pairs are optional. The value is treated as a single string and must be formatted accordingly. If a custom key is specified in the Group by Fields list then the value is appended to the finding name (the key is not included). Example:SSL disabled for Webhook ID #444611302, where SSL disabled for Webhook is the value of the Finding Name field and ID #444611302 is the value of a custom key.
Otherwise, both the key and the value are listed at the end of the finding summary on a new line for each pair. Example: Score: 4.10.

